- Download Microsoft Remote Desktop Application
- Microsoft Remote Desktop Connect To Linux
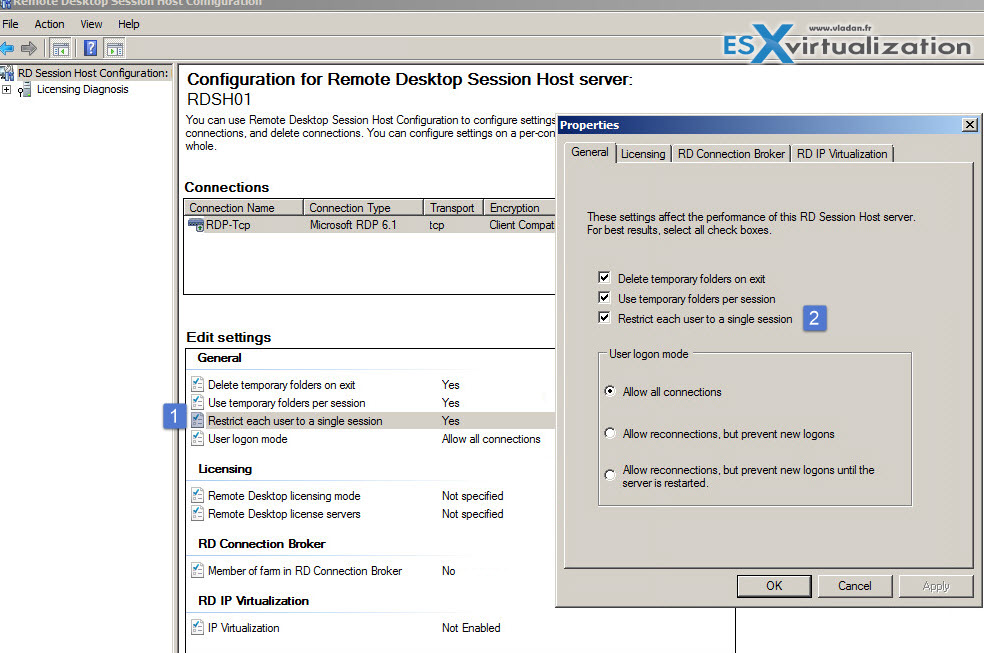
- Microsoft Remote Desktop Config
- Microsoft Remote Desktop Assistant
- Windows Remote Desktop Configuration File
- Microsoft Remote Desktop Configuration Tool
Applies to: Windows 10, Windows 8.1, Windows Server 2019, Windows Server 2016, Windows Server 2012 R2
Download Microsoft Remote Desktop Application
You can use Remote Desktop to connect to and control your PC from a remote device by using a Microsoft Remote Desktop client (available for Windows, iOS, macOS and Android). When you allow remote connections to your PC, you can use another device to connect to your PC and have access to all of your apps, files, and network resources as if you were sitting at your desk.
If the Remote Desktop app is currently open, close it. Open File Explorer (Win+E), copy and paste the folder location below for what you want to backup into the address bar of File Explorer, and press Enter. Microsoft Remote Desktop Services RDS allows users to access centralized applications and workstations in the data center remotely. Microsoft RDS is the new expanded and renamed Microsoft Terminal Services. In this post I will document the implementation of RDS in my home lab using an ‘all-in-one’ configuration. VBoring Blog Series. You can also skip the VPN and expose the Remote Desktop server directly to the Internet by setting your router to forward Remote Desktop traffic to the PC being accessed. Obviously, doing this opens you up to potential attacks over the internet, so if you go this route you’ll want to understand the risks.
Note
You can use Remote Desktop to connect to Windows 10 Pro and Enterprise, Windows 8.1 and 8 Enterprise and Pro, Windows 7 Professional, Enterprise, and Ultimate, and Windows Server versions newer than Windows Server 2008. You can't connect to computers running a Home edition (like Windows 10 Home).
To connect to a remote PC, that computer must be turned on, it must have a network connection, Remote Desktop must be enabled, you must have network access to the remote computer (this could be through the Internet), and you must have permission to connect. For permission to connect, you must be on the list of users. Before you start a connection, it's a good idea to look up the name of the computer you're connecting to and to make sure Remote Desktop connections are allowed through its firewall.
How to enable Remote Desktop
The simplest way to allow access to your PC from a remote device is using the Remote Desktop options under Settings. Since this functionality was added in the Windows 10 Fall Creators update (1709), a separate downloadable app is also available that provides similar functionality for earlier versions of Windows. You can also use the legacy way of enabling Remote Desktop, however this method provides less functionality and validation.
Windows 10 Fall Creator Update (1709) or later
You can configure your PC for remote access with a few easy steps.
- On the device you want to connect to, select Start and then click the Settings icon on the left.
- Select the System group followed by the Remote Desktop item.
- Use the slider to enable Remote Desktop.
- It is also recommended to keep the PC awake and discoverable to facilitate connections. Click Show settings to enable.
- As needed, add users who can connect remotely by clicking Select users that can remotely access this PC.
- Members of the Administrators group automatically have access.
- Make note of the name of this PC under How to connect to this PC. You'll need this to configure the clients.
Windows 7 and early version of Windows 10
To configure your PC for remote access, download and run the Microsoft Remote Desktop Assistant. This assistant updates your system settings to enable remote access, ensures your computer is awake for connections, and checks that your firewall allows Remote Desktop connections.
All versions of Windows (Legacy method)
To enable Remote Desktop using the legacy system properties, follow the instructions to Connect to another computer using Remote Desktop Connection.
Should I enable Remote Desktop?
If you only want to access your PC when you are physically using it, you don't need to enable Remote Desktop. Enabling Remote Desktop opens a port on your PC that is visible to your local network. You should only enable Remote Desktop in trusted networks, such as your home. You also don't want to enable Remote Desktop on any PC where access is tightly controlled.
Be aware that when you enable access to Remote Desktop, you are granting anyone in the Administrators group, as well as any additional users you select, the ability to remotely access their accounts on the computer.
You should ensure that every account that has access to your PC is configured with a strong password.
Why allow connections only with Network Level Authentication?
If you want to restrict who can access your PC, choose to allow access only with Network Level Authentication (NLA). When you enable this option, users have to authenticate themselves to the network before they can connect to your PC. Allowing connections only from computers running Remote Desktop with NLA is a more secure authentication method that can help protect your computer from malicious users and software. To learn more about NLA and Remote Desktop, check out Configure NLA for RDS Connections.
If you're remotely connecting to a PC on your home network from outside of that network, don't select this option.
-->For Windows Remote Management (WinRM) scripts to run, and for the Winrm command-line tool to perform data operations, Windows Remote Management (WinRM) has to be both installed and configured.
These elements also depend on WinRM configuration.
- The Windows Remote Shell command-line tool (Winrs).
- Event forwarding.
- Windows PowerShell 2.0 remoting.
Where WinRM is installed
WinRM is automatically installed with all currently-supported versions of the Windows operating system.
Configuration of WinRM and IPMI
These WinRM and Intelligent Platform Management Interface (IPMI)WMI provider components are installed with the operating system.
- The WinRM service starts automatically on Windows Server 2008 and on wards (on Windows Vista, you need to start the service manually).
- By default, no WinRM listener is configured. Even if the WinRM service is running, WS-Management protocol messages that request data can't be received nor sent.
- Internet Connection Firewall (ICF) blocks access to ports.
Use the Winrm command to locate listeners and the addresses by typing the following command at a command prompt.
To check the state of configuration settings, type the following command.
Quick default configuration
You can enable the WS-Management protocol on the local computer, and set up the default configuration for remote management with the command winrm quickconfig.
The winrm quickconfig command (or the abbreviated version winrm qc) performs these operations.
- Starts the WinRM service, and sets the service startup type to auto-start.
- Configures a listener for the ports that send and receive WS-Management protocol messages using either HTTP or HTTPS on any IP address.
- Defines ICF exceptions for the WinRM service, and opens the ports for HTTP and HTTPS.
Note
The winrm quickconfig command creates a firewall exception only for the current user profile. If the firewall profile is changed for any reason, you should run winrm quickconfig to enable the firewall exception for the new profile; otherwise, the exception might not be enabled.

To retrieve information about customizing a configuration, type winrm help config at a command prompt.
To configure WinRM with default settings
Type
winrm quickconfigat a command prompt.If you're not running under the local computer Administrator account, then you must either select Run as Administrator from the Start menu, or use the Runas command at a command prompt.
When the tool displays Make these changes [y/n]?, type y.
If configuration is successful, then the following output is displayed.
Keep the default settings for client and server components of WinRM, or customize them. For example, you might need to add certain remote computers to the client configuration TrustedHosts list.
You should set up a trusted hosts list when mutual authentication can't be established. Kerberos allows mutual authentication, but it can't be used in workgroups—only domains. A best practice when setting up trusted hosts for a workgroup is to make the list as restricted as possible.
Create an HTTPS listener by typing the command
winrm quickconfig -transport:https. Be aware that you must open port 5986 for HTTPS transport to work.
Listener and WS-Management protocol default settings
To get the listener configuration, type winrm enumerate winrm/config/listener at a command prompt. Listeners are defined by a transport (HTTP or HTTPS) and an IPv4 or IPv6 address.
winrm quickconfig creates the following default settings for a listener. You can create more than one listener. For more information, type winrm help config at a command prompt.
Address
Specifies the address for which this listener was created.
Transport
Specifies the transport to use to send and receive WS-Management protocol requests and responses. The value must be either HTTP or HTTPS. The default is HTTP.
Port
Specifies the TCP port for which this listener is created.
WinRM 2.0: The default HTTP port is 5985.
Hostname
Specifies the host name of the computer on which the WinRM service is running. The value must be a fully-qualified domain name, or an IPv4 or IPv6 literal string, or a wildcard character.
Enabled
Specifies whether the listener is enabled or disabled. The default value is True.
URLPrefix
Specifies a URL prefix on which to accept HTTP or HTTPS requests. This is a string containing only the characters a-z, A-Z, 9-0, underscore (_), and slash (/). The string must not start with or end with a slash (/). For example, if the computer name is SampleMachine, then the WinRM client would specify https://SampleMachine/<URLPrefix> in the destination address. The default URL prefix is 'wsman'.
CertificateThumbprint
Specifies the thumbprint of the service certificate. This value represents a string of two-digit hexadecimal values found in the Thumbprint field of the certificate. This string contains the SHA-1 hash of the certificate. Certificates are used in client certificate-based authentication. Certificates can be mapped only to local user accounts, and they do not work with domain accounts.
ListeningOn
Specifies the IPv4 and IPv6 addresses that the listener uses. For example: '111.0.0.1, 111.222.333.444, ::1, 1000:2000:2c:3:c19:9ec8:a715:5e24, 3ffe:8311:ffff:f70f:0:5efe:111.222.333.444, fe80::5efe:111.222.333.444%8, fe80::c19:9ec8:a715:5e24%6'.
Protocol default settings
Many of the configuration settings, such as MaxEnvelopeSizekb or SoapTraceEnabled, determine how the WinRM client and server components interact with the WS-Management protocol. The following list describes the available configuration settings.
MaxEnvelopeSizekb
Specifies the maximum Simple Object Access Protocol (SOAP) data in kilobytes. The default is 150 kilobytes.
Note
The behavior is unsupported if MaxEnvelopeSizekb is set to a value greater than 1039440.
MaxTimeoutms
Specifies the maximum time-out, in milliseconds, that can be used for any request other than Pull requests. The default is 60000.
MaxBatchItems
Specifies the maximum number of elements that can be used in a Pull response. The default is 32000.
MaxProviderRequests
Specifies the maximum number of concurrent requests that are allowed by the service. The default is 25.
WinRM 2.0: This setting is deprecated, and is set to read-only.
WinRM client default configuration settings
The client version of WinRM has the following default configuration settings.
NetworkDelayms
Specifies the extra time in milliseconds that the client computer waits to accommodate for network delay time. The default is 5000 milliseconds.
URLPrefix
Specifies a URL prefix on which to accept HTTP or HTTPS requests. The default URL prefix is 'wsman'.
AllowUnencrypted
Allows the client computer to request unencrypted traffic. By default, the client computer requires encrypted network traffic and this setting is False.
Basic
Allows the client computer to use Basic authentication. Basic authentication is a scheme in which the user name and password are sent in clear text to the server or proxy. This method is the least secure method of authentication. The default is True.
Digest
Allows the client to use Digest authentication. Digest authentication is a challenge-response scheme that uses a server-specified data string for the challenge. Only the client computer can initiate a Digest authentication request. The client computer sends a request to the server to authenticate, and receives a token string from the server. Then the client computer sends the resource request, including the user name and a cryptographic hash of the password combined with the token string. Digest authentication is supported for HTTP and for HTTPS. WinRM Shell client scripts and applications can specify Digest authentication, but the WinRM service does not accept Digest authentication. The default is True.
Note
Digest authentication over HTTP is not considered secure.
Certificate
Allows the client to use client certificate-based authentication. Certificate-based authentication is a scheme in which the server authenticates a client identified by an X509 certificate. The default is True.
Kerberos
Allows the client to use Kerberos authentication. Kerberos authentication is a scheme in which the client and server mutually authenticate by using Kerberos certificates. The default is True.
Negotiate
Allows the client to use Negotiate authentication. Negotiate authentication is a scheme in which the client sends a request to the server to authenticate. The server determines whether to use the Kerberos protocol or NTLM. The Kerberos protocol is selected to authenticate a domain account, and NTLM is selected for local computer accounts. The user name must be specified in domainuser_name format for a domain user. The user name must be specified in 'server_nameuser_name' format for a local user on a server computer. The default is True.
CredSSP
Allows the client to use Credential Security Support Provider (CredSSP) authentication. CredSSP enables an application to delegate the user's credentials from the client computer to the target server. The default is False.
DefaultPorts
Specifies the ports that the client will use for either HTTP or HTTPS.
WinRM 2.0: The default HTTP port is 5985, and the default HTTPS port is 5986.
TrustedHosts
Specifies the list of remote computers that are trusted. Other computers in a workgroup or computers in a different domain should be added to this list.
Note
The computers in the TrustedHosts list are not authenticated. The client may send credential information to these computers.
If an IPv6 address is specified for a TrustedHost, the address must be enclosed in square brackets as demonstrated by the following winrm utility command: winrm set winrm/config/client '@{TrustedHosts ='[0:0:0:0:0:0:0:0]'}'.
For more info about how to add computers to the TrustedHosts list, type winrm help config.
WinRM service default configuration settings
The service version of WinRM has the following default configuration settings.
RootSDDL
Specifies the security descriptor that controls remote access to the listener. The default is 'O:NSG:BAD:P(A;;GA;;;BA)(A;;GR;;;ER)S:P(AU;FA;GA;;;WD)(AU;SA;GWGX;;;WD)'.
MaxConcurrentOperations
The maximum number of concurrent operations. The default is 100.
WinRM 2.0: The MaxConcurrentOperations setting is deprecated, and is set to read-only. This setting has been replaced by MaxConcurrentOperationsPerUser.
MaxConcurrentOperationsPerUser
Specifies the maximum number of concurrent operations that any user can remotely open on the same system. The default is 1500.
EnumerationTimeoutms
Specifies the idle time-out in milliseconds between Pull messages. The default is 60000.
MaxConnections
Specifies the maximum number of active requests that the service can process simultaneously. The default is 300.
WinRM 2.0: The default is 25.
MaxPacketRetrievalTimeSeconds
Specifies the maximum length of time, in seconds, the WinRM service takes to retrieve a packet. The default is 120 seconds.
AllowUnencrypted
Allows the client computer to request unencrypted traffic. The default is False.
Basic
Allows the WinRM service to use Basic authentication. The default is False.
Certificate
Allows the WinRM service to use client certificate-based authentication. The default is False.
Kerberos
Allows the WinRM service to use Kerberos authentication. The default is True.
Negotiate
Allows the WinRM service to use Negotiate authentication. The default is True.
CredSSP
Allows the WinRM service to use Credential Security Support Provider (CredSSP) authentication. The default is False.
CbtHardeningLevel
Sets the policy for channel-binding token requirements in authentication requests. The default is Relaxed.
DefaultPorts
Specifies the ports that the WinRM service will use for either HTTP or HTTPS.
WinRM 2.0: The default HTTP port is 5985, and the default HTTPS port is 5986.
IPv4Filter and IPv6Filter
Specifies the IPv4 or IPv6 addresses that listeners can use. The defaults are IPv4Filter = * and IPv6Filter = *.
IPv4: An IPv4 literal string consists of four dotted decimal numbers, each in the range 0 through 255. For example: 192.168.0.0.
IPv6: An IPv6 literal string is enclosed in brackets and contains hexadecimal numbers that are separated by colons. For example: [::1] or [3ffe:ffff::6ECB:0101].
EnableCompatibilityHttpListener
Specifies whether the compatibility HTTP listener is enabled. If this setting is True, then the listener will listen on port 80 in addition to port 5985. The default is False.
EnableCompatibilityHttpsListener
Specifies whether the compatibility HTTPS listener is enabled. If this setting is True, then the listener will listen on port 443 in addition to port 5986. The default is False.
Winrs Default Configuration Settings
winrm quickconfig also configures Winrs default settings.
AllowRemoteShellAccess
Enables access to remote shells. If you set this parameter to False, then new remote shell connections will be rejected by the server. The default is True.
IdleTimeout
Specifies the maximum time, in milliseconds, that the remote shell will remain open when there is no user activity in the remote shell. The remote shell is automatically deleted after the time that is specified.
WinRM 2.0: The default is 180000. The minimum value is 60000. Setting this value lower than 60000 will have no effect on the time-out.
MaxConcurrentUsers
Specifies the maximum number of users who can concurrently perform remote operations on the same computer through a remote shell. New remote shell connections will be rejected if they exceed the specified limit. The default is 5.
MaxShellRunTime
Specifies the maximum time, in milliseconds, that the remote command or script is allowed to execute. The default is 28800000.
WinRM 2.0: The MaxShellRunTime setting is set to read-only. Changing the value for MaxShellRunTime will have no effect on the remote shells.
MaxProcessesPerShell
Specifies the maximum number of processes that any shell operation is allowed to start. A value of 0 allows for an unlimited number of processes. The default is 15.
MaxMemoryPerShellMB
Specifies the maximum amount of memory allocated per shell, including the shell's child processes. The default is 150 MB.
Microsoft Remote Desktop Connect To Linux
MaxShellsPerUser
Specifies the maximum number of concurrent shells that any user can remotely open on the same computer. If this policy setting is enabled, then the user won't be able to open new remote shells if the count exceeds the specified limit. If this policy setting is disabled or is not configured, the limit will be set to 5 remote shells per user by default.
Configuring WinRM with Group Policy
Use the Group Policy editor to configure Windows Remote Shell and WinRM for computers in your enterprise.
To configure with Group Policy
- Open a Command Prompt window as an administrator.
- At the Command Prompt, type
gpedit.msc. The Group Policy Object Editor window opens. - Find the Windows Remote Management and Windows Remote Shell Group Policy Objects (GPO) under Computer ConfigurationAdministrative TemplatesWindows Components.
- On the Extended tab, select a setting to see a description. Double click a setting to edit it.
Windows Firewall and WinRM 2.0 ports
Starting in WinRM 2.0, the default listener ports configured by Winrm quickconfig are port 5985 for HTTP transport, and port 5986 for HTTPS. WinRM listeners can be configured on any arbitrary port.
If a computer is upgraded to WinRM 2.0, the previously configured listeners are migrated, and still receive traffic.
WinRM installation and configuration notes
WinRM isn't dependent on any other service except WinHttp. If the IIS Admin Service is installed on the same computer, then you might see messages that indicate that WinRM can't be loaded before Internet Information Services (IIS). However, WinRM doesn't actually depend on IIS—those messages occur because the load order ensures that the IIS service starts before the HTTP service. WinRM does require that WinHTTP.dll be registered.
If the ISA2004 firewall client is installed on the computer, then it can cause a Web Services for Management (WS-Management) client to stop responding. To avoid this issue, install ISA2004 Firewall SP1.
If two listener services with different IP addresses are configured with the same port number and computer name, then WinRM listens or receives messages on only one address. This is because the URL prefixes used by the WS-Management protocol are the same.
IPMI driver and provider installation notes
The driver might not detect the existence of IPMI drivers that are not from Microsoft. If the driver fails to start, then you might need to disable it.
If the baseboard management controller (BMC) resources appear in the system BIOS, then ACPI (Plug and Play) detects the BMC hardware, and automatically installs the IPMI driver. Plug and Play support might not be present in all BMCs. If the BMC is detected by Plug and Play, then an Unknown Device appears in Device Manager before the Hardware Management component is installed. When the driver is installed, a new component, the Microsoft ACPI Generic IPMI Compliant Device, appears in Device Manager.
If your system doesn't automatically detect the BMC and install the driver, but a BMC was detected during the setup process, then you must create the BMC device. To do this, type the following command at a command prompt: Rundll32 ipmisetp.dll, AddTheDevice. After this command is executed, the IPMI device is created, and it appears in Device Manager. If you uninstall the Hardware Management component, then the device is removed.
For more information, see Hardware Management Introduction.
Microsoft Remote Desktop Config
The IPMI provider places the hardware classes in the roothardwarenamespace of WMI. For more information about the hardware classes, see IPMI Provider. For more information about WMI namespaces, see WMI Architecture.
Microsoft Remote Desktop Assistant
WMI plug-in configuration notes
Windows Remote Desktop Configuration File
Beginning with Windows 8 and Windows Server 2012, WMI plug-ins have their own security configurations. For a normal or power (non-administrator) user to be able to use the WMI plug-in, you need to enable access for that user after the listener has been configured. First, you must set up the user for remote access to WMI through one of these steps.
Microsoft Remote Desktop Configuration Tool
- Run
lusrmgr.mscto add the user to the WinRMRemoteWMIUsers__ group in the Local Users and Groups window, or - use the winrm command-line tool to configure the security descriptor for the namespace of the WMI plug-in, as follows:
winrm configSDDL http://schemas.microsoft.com/wbem/wsman/1/wmi/ WmiNamespace.
When the user interface appears, add the user.
After setting up the user for remote access to WMI, you must set up WMI to allow the user to access the plug-in. To do this, run wmimgmt.msc to modify the WMI security for the namespace to be accessed in the WMI Control window.
The majority of the WMI classes for management are in the rootcimv2 namespace.
